Authentication is the process of verifying who you are. So In this article, I will explain What is Authentication and Authorization, and methods of Authentication like passwords, biometrics, etc.
What are Authentication and Authorization?
Authentication and Authorization both are processes to protect your privacy, data, etc. Authentication is the process of verifying who you are. This usually involves a username and a password but can include any other method of demonstrating identities, such as a smart card, retina scan, voice recognition, or fingerprints. Authentication is equivalent to showing your driving license at the ticket counter at the airport.
Authorization is the function to access the right resource, like when you log in your the computer you just type your password, So Here the Password is Authentication and the function to log in is Authorization.
Authentication Methods:
- Passwords
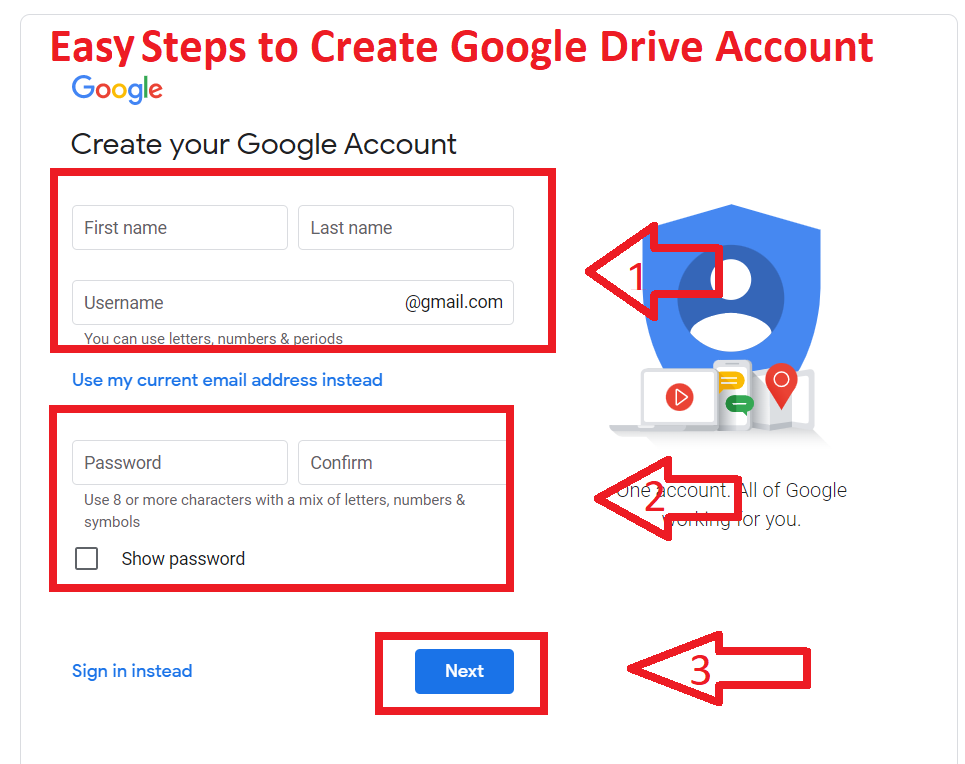
Passwords are the most widely used form of authentication. Users provide an identifier, a typed word or phrase, or perhaps a token card, along with a password. Therefore, In many systems, the password, on the host itself, is not stored as plain text but is encrypted. Password authentication does not normally require complicated or robust hardware since the authentication of this type is in general simple and does not require much processing power.
Read More: Good and Bad Side of the Internet
-
Digital Signatures
A digital signature is an electronic signature. Therefore, that can be used to authenticate the identity of the sender of a message or the signer of a document, and possibly to ensure that the original content of the message or document that has been sent is unchanged. A digital signature can be sure of the sender’s identity and that the message arrived intact. A digital certificate contains the digital signature of the certificate-issuing authority so that anyone can verify that the certificate is real.
-
Biometric
In this authentication process, users may biometrically authenticate via their fingerprint or iris scan using provided hardware and then enter a PIN or Password. However, while this type of authentication is suitable in limited applications, this solution may become unacceptably slow and comparatively expansive. It may easily be replayed unless the reader is completely secure and guarded.
Read More: What is Cyber Crime
- Magnetic Cards
Credit cards, debit cards, ATM cards, etc combined with secure, encrypting card readers provide a possible solution for two-factor/strong authentication. Each magnetic stripe card has unique characteristics much like the card’s own fingerprint called a magnetic fingerprint. The advantage is that a magnetic fingerprint already exists on every magnetic stripe card because it is an intrinsic characteristic and no cards would need to be re-issued.
Similarly, Each swipe of the card provides a correlative number called a dynamic digital identifier. So which use for scored and “matched” to the originating value to determine the card’s authenticity. It des a special reader that can read the magnetic fingerprint value.
-
Smart Card
The smart card is a pocket-sized integrated circuit card (ICC) that can process data. There are two broad categories of these cards. Money cards contain only non-volatile memory storage components, and perhaps some specific security logic. Microprocessor cards contain volatile memory and microprocessor components. To make a Smart card most of the time uses PVC, but sometimes uses ABS. Using smart cards is also a form of strong security authentication for single sign-on within large companies and Organizations.
Other Common Used Authentication methods are USB Tokens, Mobile Signatures, Digital Certificates, etc.
I hope you get the all information about Authentication and Authorization, Digital signatures, biometrics. If you like this article, you can share and comment. So that we too have a chance to learn something from your ideas and improve something.
Read Also: